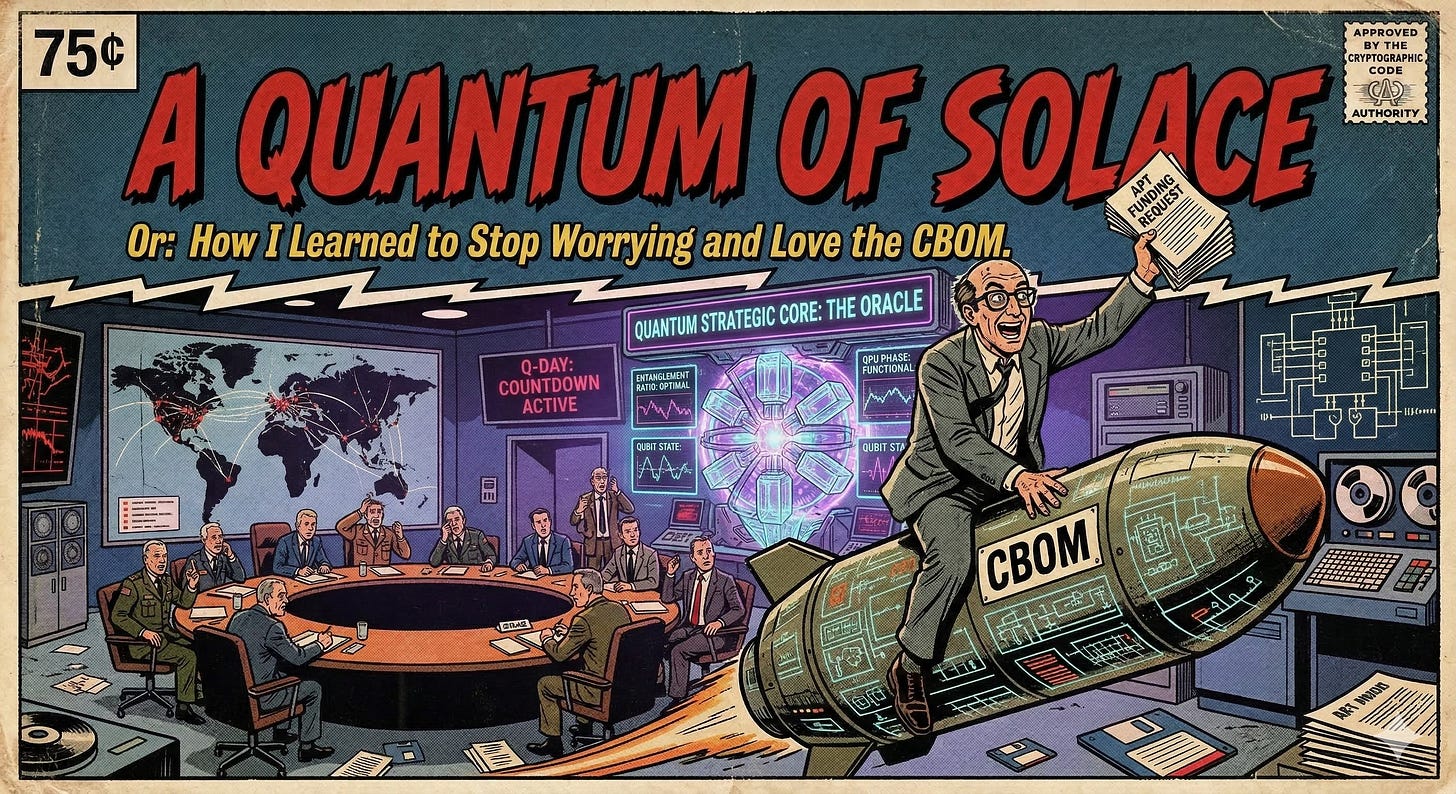
A Quantum of Solace
Or: How I Learned to Stop Worrying and Love the CBOM
Nobody selling PQC readiness has run the HNDL business case from the adversary’s budget office. What follows is the exercise the industry skipped: the funding request it would have to be, from a fictional signals intelligence directorate targeting global financial infrastructure. The scope is bulk confidentiality-in-transit; signature ecosystems, data-at-rest, and long-lived artifacts are separate problem classes addressed in the companion piece. The math is real. The sources are cited. The bureaucratic infighting is extrapolated from universal principles.
MINISTRY OF STATE SECURITY — SIGNALS INTELLIGENCE DIRECTORATE
CLASSIFICATION: DRAGON JADE / COMPARTMENTED
MEMORANDUM FOR: Standing Committee on Intelligence Resource Allocation
FROM: Deputy Director, Long-Horizon Signals Collection (Unit 4128)
RE: Project GLASS CATHEDRAL — Harvest Now, Decrypt Later Infrastructure Investment
Unit 4128 requests approval for GLASS CATHEDRAL: a passive signals collection program targeting financial infrastructure, with decryption upon availability of a cryptographically relevant quantum computer (CRQC). Requested funding: $300M–$500M for collection infrastructure, plus $500M–$5B for quantum decryption. Division 3 (Human Intelligence) has submitted a competing proposal for $54M. Much of the collection infrastructure described here already exists within the Ministry under other directorates.
The HNDL narrative, as articulated by the enterprise security industry, is notable for what it declines to specify. “Nation-states are harvesting your encrypted traffic” — but through what infrastructure, at what cost, with what coverage? The industry treats collection as an assumed given and proceeds directly to quantum timelines, because specifying a collection architecture invites the analysis that follows. Unit 4128 will now do the work the vendors prefer to leave as an exercise for the reader.
Collection. Most collection is nearly free — sovereign border gateways, allied nation access, geographic chokepoints.1 Even with all available tiers operational, the aperture captures only cross-border traffic — SWIFT, correspondent banking, market data feeds, offshore branch communications. The fraction containing the most sensitive material — trading strategies, risk models, board deliberations — largely does not traverse externally observable paths. Storage is trivial: $8–15M over twenty years.
Decryption. Estimates for breaking RSA-2048 have improved from ~20M physical qubits to under 100K using QLDPC architectures — but 100K qubits factors one key per month. Practical throughput — roughly three key-breaks per day — requires approximately one million qubits.22 The Committee should attend not to the qubit count but to the throughput.
The forward secrecy cliff. Without forward secrecy (static RSA), three keys per day against 1,000–50,000 server certificates takes one to forty-six years. Expensive, slow, but conceivable. With forward secrecy (TLS 1.3 / ECDHE), each session requires an independent quantum computation. One day of wire data: 913,000 CRQC-years. Selective collection reduces volume; it does not change the unit cost — where forward secrecy is enforced, each session requires its own computation whether collected selectively or in bulk.3
Risk factors. If CRQC arrives later or at higher cost, the archive accrues storage cost with no return — in venture capital terminology, a “pre-revenue phase” of unlimited duration. Financial transactions have limited shelf life; a twenty-year-old wire transfer record reveals that Bank A paid Bank B $47M on a Tuesday in 2025. The strategic value of this in 2045 is, with great respect to the Committee, not self-evident. Division 3 notes that their assets can tell us why the wire was sent, who approved it, and what it means — this Thursday. Meanwhile, TLS 1.3 mandates forward secrecy; every endpoint that migrates moves from Scenario A to Scenario B. We are betting the global banking sector will fail to complete a configuration change for which the standards have existed since 2018. This is perhaps the most defensible assumption in the entire proposal.4
The alternative. Division 3’s Project WARM HANDSHAKE: four recruited insiders, $40M over twenty years. Continuous, curated, targeted intelligence with no latency and no dependence on a machine that does not exist. Meanwhile, initial access brokers sell Domain Admin for $500–$50K — falling by half every five years.
The recursive dependency. Bulk collection is indiscriminate — making the archive tractable requires targeting selectors not available from external observation. The capability that makes the archive searchable is the same capability Division 3 provides, at which point the archive is redundant. We acknowledge that “comprehensive record of undifferentiated encrypted traffic, decryptable at a cost exceeding most national GDPs, from sessions whose plaintext could have been obtained by asking Gerald in Network Operations” is a difficult sentence to put in a funding request.
Recommendation. Unit 4128 recommends that the Committee fund GLASS CATHEDRAL at the requested level, because it is our job to present collection options for Committee decision. The Committee should fund whatever it considers most appropriate.5
STANDING COMMITTEE ON INTELLIGENCE RESOURCE ALLOCATION — OFFICE OF THE CHAIRMAN
RE: Project GLASS CATHEDRAL — Disposition
We will stipulate Unit 4128’s most optimistic projections. We accept the QLDPC qubit threshold, the cost range, the 2030s timeline. We are generous on precisely the question the enterprise security industry considers most important: when will the machine exist?
It does not help.
Three key-breaks per day. Forty-six years for the certificate inventory. The intelligence produced — decrypted financial transactions from the 2020s, available in the 2080s — is of a vintage the Bureau of Historical Intelligence Assessment has declined to characterize. Under forward secrecy, one day of wire data requires 913,000 years on a single machine. A fleet of a thousand CRQCs — $500B–$5T — processes one day in 913 years. The Committee does not typically fund programs with a time-to-intelligence measured in centuries.
We note, for context, that a significant equity position in the target institution costs less than a single CRQC and yields complete, real-time access to everything GLASS CATHEDRAL promises to deliver in 2080. We mention this not as a proposal but as a unit of measurement. Division 3 delivers equivalent intelligence on Thursday.
GLASS CATHEDRAL is declined. The cost analysis was acceptable. The throughput analysis was not.
WARM HANDSHAKE is approved. $54 million.
The Committee prefers a simpler formulation than the Bureau of Logical Consistency’s “recursive dependency”: GLASS CATHEDRAL requires Division 3’s cooperation to succeed, and Division 3’s cooperation makes GLASS CATHEDRAL redundant. We are informed that in software engineering this is called a “circular dependency.” We are informed that it is not a compliment. The Committee trusts that the next submission will not depend on Gerald in Network Operations for its operational feasibility.
The Committee has approved a one-time allocation for Unit 4128’s holiday party to be held at a venue other than the Building 9 cafeteria. This should not be interpreted as a consolation. It is a consolation.
GLASS CATHEDRAL is fiction. The math is not. Every quantum projection uses the most optimistic credible scenario and should be read as lower bounds. Argue the figures if you like; the scaling law is what kills the program — forward secrecy converts “break one key per server” to “break one key per session,” and absent protocol collapse into shared secrets (PSK resumption, ticket key compromise, endpoint leakage), no improvement in quantum hardware changes that scaling. The operational playbook is in A Prepper’s Guide to Q Day. But none of it functions without a complete cryptographic bill of materials. You can’t rotate what you can’t find. The CBOM is the unglamorous deliverable that makes everything else possible. Learn to love it.
The adversary funds both paths: identity for speed, harvest for durability. Collection is cheap and the archive is cheap — the question is whether the option exercises at scale against modern FS endpoints before the intelligence decays. The identity path costs $2,700 and arrives on Thursday. The harvest path costs billions, processes three keys per day, and works only against endpoints that failed to enforce a configuration change standardized in 2018. Fund accordingly.
We are informed that the international press refers to cooperative lawful intercept infrastructure as “surveillance concerns.” We refer to it as “existing collection capability requiring no new appropriation.”
The most aggressive qubit estimate (Webster et al., 2026) comes from a quantum computing startup, assumes undemonstrated hardware parameters, and defers the decoder problem. We cite it because our mandate is to present the most optimistic credible scenario.
The billion-session figure represents total GSIB traffic volume; our cross-border collection aperture captures an estimated 5–15% of this. The analysis uses the full volume as the upper bound — at the actual fraction, these figures reduce by roughly an order of magnitude without changing the conclusion. For experimental validation of the per-session cost model across TLS 1.2, TLS 1.3, QUIC, and SSH, see Blanco-Romero et al., 2026. TLS 1.3 PSK resumption creates chain dependencies that further reduce the effective independent computations.
The enterprise security industry’s track record on timely configuration changes is reassuring. See: SHA-1 deprecation (7 years), TLS 1.0 deprecation (ongoing, 16+ years), IPv6 adoption (ongoing, 26 years). Unit 4128 considers this the strongest pillar of the GLASS CATHEDRAL business case.
Unit 4128’s annual holiday party has been held at the cafeteria in Building 9 for eleven consecutive years. Division 3 held theirs last year at [REDACTED]. We mention this only for context.